WHAT IS PERIMETER SECURITY?
Historically, perimeter security mostly refers to the protection of high-risk sites such as military facilities and critical national infrastructure as a response to serious threats like violent assaults, targeted threats and in worst cases, terrorist attacks.
However, advancements in technology and manufacturing capabilities have broadened the applications of perimeter security, expanding into more common sectors like commercial, retail, transportation, and even residential applications.
The purpose of perimeter security is to safeguard people and assets within a defined space by preventing unauthorised physical access by the use of integrated elements and systems, both electronic and mechanical.
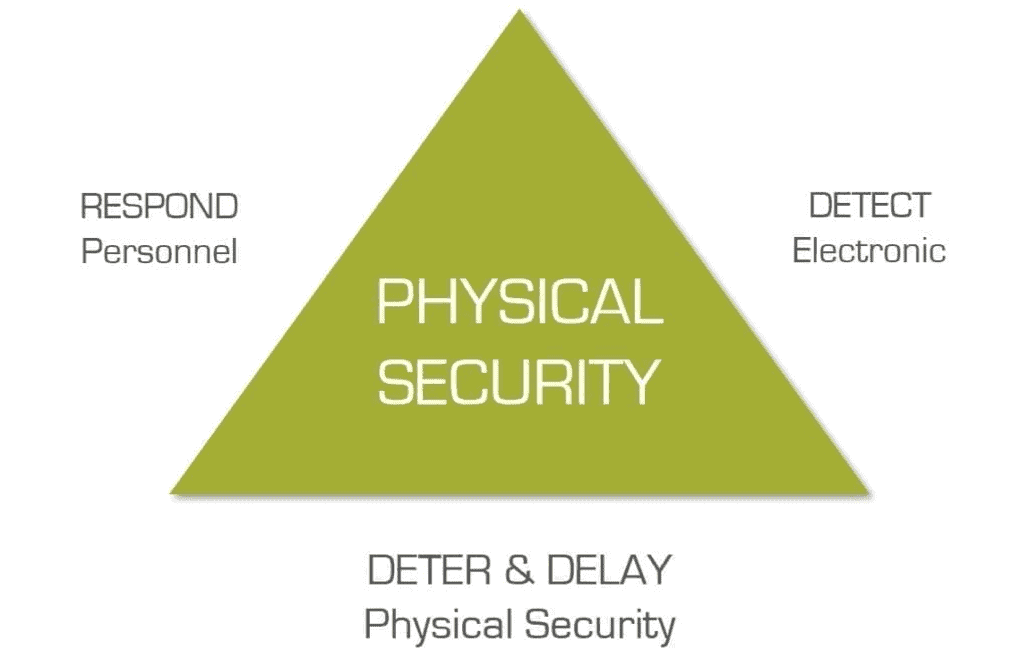
Within the physical security industry, there is a common understanding; the best method of security is based on a layered model of various security measures that serve to deter, detect, and delay intrusions.
TYPES OF THREAT
Depending on the type of application and the assets contained within, the type of threats to perimeter security will vary. Below we have listed several types of threat that will cover all scenarios:
- Intrusion / trespassing
- Damage to property
- Protests from activists
- Espionage
- Vandalism
- Theft
- Harassment
- Targeted threats
- Vehicle theft or damage
- Proximity to high-risk locations (government, financial institutions, high-net worth individuals, etc.)
- Terrorist attacks
If you require advice about any of the information within this post, please do not hesitate to get in touch using the form below.
TIPS FOR BETTER PERIMETER SECURITY
When planning and implementing perimeter security, there are a few underlying factors we recommend reviewing.
The first is visibility. Is the security measure you are considering visible to deter intruders? Is it aesthetically appropriate for the application? On the other end, as a rule of thumb, it is important to hide critical assets away from easy sight.
Carry out research into local information and statistics such as levels of crime and proximity of first-responder parties.
Don’t underestimate environmental conditions. Whichever perimeter security tool you opt for, make sure it is able to withstand conditions such as extreme cold or heat, heavy rain, snow, fog, and lighting. These are common issues with CCTV systems, for example.
No security measure will serve its purpose if attackers are easily able to cut off the power source and render them useless. We highly recommend opting for battery backups. This will provide effective security 24h a day even in the case of power loss.
Looking further ahead, you should also look into how you will respond to an intrusion. Are responders appropriately trained and equipped?
PERIMETER SECURITY TOOLS
The type of perimeter security tools and systems you need will depend on the likely intrusion risks and type of application. Here is a list of the most common measures:
- Video surveillance
- Alarm systems
- Intrusion detection systems (motion sensors, microwave, etc)
- Access control
- Lighting
- Fences and gates
- Vehicle barriers and bollards
- Security shutters*

SECURITY SHUTTERS
Security shutters are not exactly used as part of perimeter security but can provide an additional and retractable layer of protection for entrances and apertures against forced entry in conjunction with other perimeter security measures.
Serving as a durable and visible deterrent, security shutters are highly effective and can be specified for both high-risk and low-risk properties, ranging from commercial to residential, government, financial institutions, and others.
Always consider how reliable a security measure really is in preventing intrusion, make sure they meet recognised security standards such as LPS 1175.
Also, consider the materials and the finishes a product offers. This will determine performance with regards to maintenance and sensitivity to surrounding environments.